Did China’s PLA Unit 61419 purchase foreign Antivirus Products for Exploitation?
A review of another disputed threat intelligence story
Disclaimer: The views, methods, and opinions expressed at Anchored Narratives are those of the author and do not necessarily reflect the official policy or position of my employer.
Introduction
This week, some chatter on Twitter and other social media around an interesting story from the threat intelligence company Recorded Future and their Insikt Group (hereafter: Insikt Group). Their publication claims that Chinese PLA Unit 61419 is suspected of having bought multiple English versions of antivirus products from different software vendors. They allege that the products were likely bought for exploitation in potential supply chain attacks. One of the collected tweets triggered on the “PLA Unit” keywords on 6 May 2021 is displayed below.
"Chinese PLA Unit 61419 suspected to have purchased AVs for cyber-espionage https://t.co/kKE47tZSDK #APT #Intelligence #Antivirus #Cybersecurity"The above tweet leads to the original story with the title “China’s PLA Unit 61419 Purchasing Foreign Antivirus Products, Likely for Exploitation,” published on 5 May 2021 by the threat intelligence company Recorded Future. Apparently, several information professionals found the story really relevant to share. Let’s apply the Anchored Narratives Theory (ANT) to this story from the Insikt group to determine how credible this story actually is? If you have not read the article already, please do so.
A short recap of the story
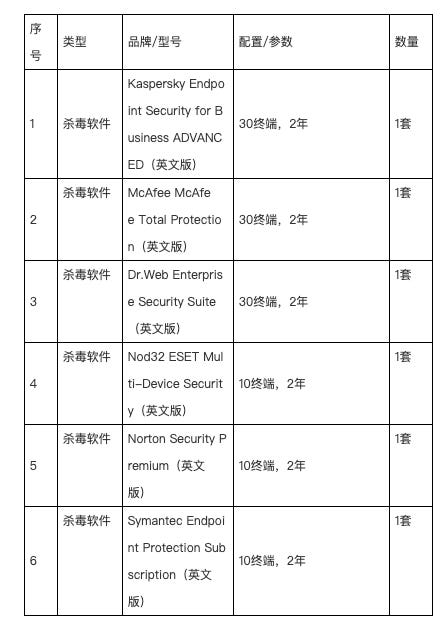
According to the article of the Insikt group, “China’s PLA Unit 61419” bought multiple English antivirus products ranging from Kaspersky to Symantec. According to their assessment, the purchase of foreign antivirus software by the PLA Unit poses a high risk to the global antivirus software supply chain. They state that two scenarios are likely:
Scenario 1: PLA cyber units and affiliated hacking groups will use foreign antivirus programs as a testing environment for natively developed malware. They will run the malware through foreign antivirus products to test its ability to evade detection, thereby making it more likely to successfully infect its targeted victims.
Scenario 2: PLA cyber units and affiliated hacking groups will reverse engineer the foreign antivirus software code to find previously undisclosed vulnerabilities. They will then use the newly discovered vulnerabilities in a zero-day attack for initial intrusion.
The Insikt Group shares screenshots of the procured antivirus products in Chinese and English to support their assessment. Additionally, they also include a historical pattern of China’s involvement of software supply chain exploitation in multiple cyber intrusion campaigns.
Do you believe this story, and why? Is this a credible story? To assess the credibility of the article and its conclusions, one should assess the evidence on where this story is based on. Let’s assess the presented evidence.
A review of a disputed threat intelligence story by the Insikt Group
As I have explained in an earlier article (ANT), if you do not want to fell victim to a disinformation campaign, investigative stories should be constructed based on evidence and factual information. To make a credible story, the story must answer the simple basic Who, What, Why, When, Where, How questions. Presented evidence must hold three core properties, namely relevance, credibility, and probative force.1 For tangible evidence, DNA evidence, documents, and files (digital evidence), the main criteria are authenticity, correctness, and reliability.2 The detective or investigator must verify the authenticity of the evidence. Anderson et al. list three dangers to the authenticity of the evidence, namely:
the evidence may have been deliberately manipulated to mislead;
errors may have arisen in evidence or data by performing investigative actions, such as securing, transporting, and analyzing the evidence;
the witness or expert confirming the authenticity of the evidence may misinterpret or misunderstand the evidence.
Now back to the article and the evidence presented by the Recorded Future’s Insikt group. I will highlight some weaknesses found in the assessment below.
May 5, 2021 • Insikt Group®
Let’s start with the Who question? Who is the author of this article? It is unclear who the author(s) is as the article only mentions the Insikt Group. It is unclear to me why the authors of this publication remain somewhat anonymous?
Recorded Future’s Insikt Group has discovered six procurement documents from official People’s Liberation Army (PLA) military websites and other sources that show the Strategic Support Force (SSF) branch of the PLA, specifically Unit 61419, has sought to purchase antivirus software from several major American, European, and Russian security companies.
The above statement refers to six procurement documents that were obtained. But How and Where did they obtain those documents remains unclear? From which specific website(s) were these documents obtained? It remains unclear why the researchers could not share this data. To increase the credibility of the presented evidence, the article should include those details.
3.
Insikt Group has shared the above screenshot of one of the documents that details the procured anti-virus products. The original documents were not shared. Those original documents could hold forensic artifacts, so-called metadata, content, or unique values (cryptographic hashes) of the documents. These documents could be used for peer-review and to increase the credibility of the evidence and the aforementioned conclusions. So how are we able to determine where these documents come from and if the documents are authentic and not false? It remains unclear why the original documents could not be published as well? In normal malware investigations, so-called indicators of compromise are shared, which can contain those hash values. However, there can be reasons why the original documents and their sources were not published. For instance, perhaps the documents were obtained from a source that should remain anonymous, or did they (Insikt) found a flaw in the website of the PLA Unit that provides access to multiple other documents?
In an attempt to obtain the missing information necessary to value the credibility of the presented evidence, I performed reverse image searches, used OCR technology to search for the specific keywords in multiple search engines like Google, Yandex and Baidu. Still, I could not find those documents on any of the known official PLA websites or web caches.
Without being able to verify where these documents were found or assessing the authenticity of the documents, how does the reader know if these documents are authentic? Either you accept the story from the Insikt Group and anchor this story based on the presented screenshot because it seems compelling (and normally the Insikt Group shares reliable threat intelligence), or you do not accept it based on the weak presented evidence. So if you doubt the presented information, you cannot anchor on this information and need to obtain more information before you anchor it with solid evidence.
Conclusion
The assessment from the Insikt Group could be interesting. Still, the evidence presented to support their story and scenarios is fragile and does not meet any (digital) forensic standard. There could be reasons why this data was not shared in their assessment, but the article does not detail why that is the case?
The story in its current state is not credible and could even be manipulated or could serve a different intent. For scenario 1, now let’s assume the story is true. Is this activity something that only China performs, or do other nations also obtain foreign anti-virus products to test detection rates of their developed malware? There are strong indications that other nations also want to bypass anti-virus products. Furthermore, even security companies that test the security of their clients obtain multiple licenses of these products to determine if their malicious payloads are intercepted by these anti-virus or endpoint detection controls. But if the story is true, it also gives some insights into the maturity of the Chinese army on procuring software directly, not doing it covertly via a front company.
Regarding scenario 2 from the Insikt Group, it could be the case that the Chinese PLA Unit wants to reverse engineer those popular antivirus products, but this is a threat that should already be on the radar of those companies. In general, these organizations do not need a valid license for this purpose.
Personally, I believe this assessment raises more questions than the assessment itself. By answering some relevant questions, the quality of the assessment will increase and could make the story more credible. For now, the presented story is a disputed one.
T.J. Anderson, D.A. Schum & W.L. Twining (2005) Analysis of evidence (2nd ed.). Cambridge: Cambridge University Press p. 64
D.A. Schum (2005) A Wigmorean interpretation of the evaluation of a complicated pattern of evidence: Technical report, http://tinyurl.com/2a3elq